How can you ensure total protection for your company’s sensitive data?
As a European leader in data protection, Atos offers a range of hardware security modules (HSMs) that guarantee the confidentiality of your sensitive data and support your compliance with new regulations (GDPR*, PCI DSS, HIPAA, eIDAS**) throughout your digital transformation.
Our HSMs protect you from all risks of cyberattacks in connecting your equipment to virtual environments. Our data encryption range will suit every demand — from protecting hardware key management and cryptographic operations to securing information flows in large sensitive networks.
With wide-ranging technology expertise and cybersecurity R&D centers in France, Atos helps you build the secure infrastructure for an efficient, proportionate and sustainable cybersecurity policy.
Follow or contact us:
![]()
Hardware Security Modules – Trustway HSM
Data protection is a strategic step in your digital transformation journey, but most of all, it’s a priority in your company security policy.
Deploying an encryption management platform with a high level of security is essential to protect your infrastructure and data.
What is an HSM?
A hardware security module (HSM) is a physical computing device that safeguards and manages digital keys for strong authentication and provides cryptoprocessing. These modules traditionally come in the form of a plug-in card or an external device that attaches directly to a computer or network server.
HSMs and/or the cryptographic modules they employ are typically certified to internationally recognized standards such as Common Criteria or FIPS 140 to provide users with independent assurance that the design and implementation of the product and cryptographic algorithms are sound.
*Wikipedia source
Secure transport communications and data. Protecting digital assets in harsh environments.
Atos provides a rugged hardware security module (HSM) able to support the complexities and constraints of transportation to secure your data in motion or at rest.
The rugged Trustway Proteccio HSM offers secure authentication, data integrity and encryption while overcoming all the challenges of transportation systems.
How do Trustway HSMs ensure total data protection?
Compliant, flexible and innovative, our range of hardware security modules provides companies and critical infrastructures with the reliability of an innovative and robust architecture in compliance with strict security demands like GDPR, HIPAA, PCI DSS and eIDAS.
Designed to ensure the integrity and security of your cryptographic operations, our HSMs guarantee high availability and safe restore, an easy installation and an ergonomic management application.
Trustway HSM certifications
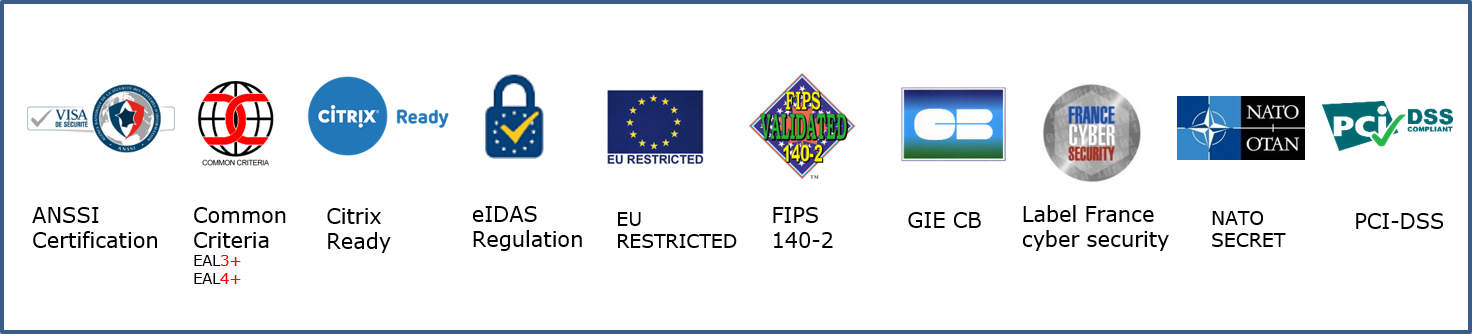
Certified high security, the Trustway hardware security module product range is completely designed (hardware and software), implemented and manufactured by Atos in France.
CC EAL4+ certification, Reinforced Qualification (ANSSI QR), NATO SECRET and EU RESTRICTED agreements covers hardware and software implementation. (FIPS 140-2 level 3 is currently in progress).
HSM Trustway Proteccio™
NetHSM
General Purpose
Innovation in security technology is the name of the game with the Trustway Proteccio™ NetHSM for data encryption. Eight independently managed cryptographic virtual HSMs sheltered in one physical HSM are made available for highly secure operational flexibility.

HSM Trustway Proteccio™
USB
General Purpose
The Trustway Proteccio™ USB offers control and security. USB connectivity allows you to maintain the sensitive environment offline in order to avoid any loss of data, and direct connectivity between your machine and the HSM. Another benefit is the rackable platform that can be easily integrated into your infrastructure.
![]()
HSM Trustway Proteccio™
OEM
General Purpose
The Trustway Proteccio™ OEM hardware security module offers the ability to deploy custom applications that are integrated then securely executed in the appliance and benefit from an easy programmability environment.

HSM Trustway Crypt2pay
Payment HSM
Trustway Crypt2pay is specially designed to secure withdrawal and payment transactions using credit, debit or store cards (authorization requests). It secures face-to-face transactions of all types, including contactless payments, as well as internet sales.
![]()
Related resources
The combined solution from Atos and DuoKey enables customers to protect their most confidential and sensitive data stored in Microsoft 365, by maintaining control of their own encryption keys.
Data protection:
-
Complete control of data privacy
-
Securely stored encrypted data and encryption keys
-
Inaccessible for third parties to access encrypted data
The combined solution from Atos and HashiCorp allows clients to securely manage and store secrets – compliant and audit safe.
Complete Control
-
Secure the Vault root key within a cryptographic boundary that uses access control mechanisms
-
Root key availability using management, storage, and redundancy features
-
Superior performance to support demanding multi-cloud applications

Factsheet
Trustway Proteccio NetHSM: Certified HSM – The root of your security
Trustway Proteccio is a hardware security module (HSM) that provides software solutions with a high-performance and highly secure environment where they can carry out their most sensitive cryptographic operations.
Brochure
Trustway HSM: Data Security – Choosing the right path through compliance
Compliant, flexible and innovative, our range of hardware security modules provides companies and critical infrastructures the reliability of an innovative and robust architecture in compliance with strict security demands.
White Paper
Download: Prevent ransomware attacks from taking down your business and defend your data
Drastic emergency situations provide a conducive environment for criminals to perform cyberattacks. Ransomware attacks today are clearly on the rise, and the risk of sensitive data being stolen from your organization is higher. Read our white paper to learn more about ransomware and how to protect your sensitive data.
Brochure
Download: Trustway GDPR Encryption, the key for data protection
Discover how Trustway’s portfolio gives organizations navigating GDPR the tools they need to solve these challenges according to the shape of their operations and their IT architecture.
News and partner program
Follow or contact us:
![]()
Technology partners
Atos’s extensive ecosystem of technology partners guarantees the confidentiality and privacy of sensitive data while ensuring compliance to increasing regulations.

Join our Club Cyber community!
Club Cyber members and partners are the core of our global ecosystem. Partners include valued resellers, distributors, software and hardware vendors, service providers, and technology partners.