How Data Security Posture Management Helps Organizations Regain Control Over Silent Data Sprawl
Data estates are growing faster than organizations can manage them. Cloud adoption, SaaS proliferation, hybrid architectures, and the rapid introduction of AI workloads have fundamentally changed how data is created, moved, and stored.
At the same time, organizations are under growing pressure from regulators, customers, and boards to demonstrate control over sensitive data. Breaches, misconfigurations, and insider exposure continue to make headlines, while geopolitical developments are adding new urgency around data sovereignty and jurisdictional accountability.
What makes this challenge particularly difficult is that it often remains invisible. Data sprawl rarely announces itself. It accumulates quietly across cloud services, collaboration platforms, shadow IT, and AI pipelines until an incident, audit, or regulatory inquiry exposes the gap.
Why traditional approaches are falling short
Many data protection strategies were designed for environments that focused on infrastructure rather than on the data-centric approach required nowadays. Periodic audits, static inventories, and perimeter centric controls struggle to keep pace with modern, dynamic infrastructure.
Several structural issues tend to surface repeatedly:
- Incomplete visibility into sensitive data
Organizations frequently underestimate how much sensitive data they hold and where it resides, particularly across SaaS platforms and unmanaged cloud services. - Rising regulatory and compliance complexity
Data protection requirements now vary significantly by geography, sector, and data type, increasing the operational burden on security and compliance teams. - Fragmented security tooling
Data protection is often disconnected from cloud security, identity, and operational monitoring, making it harder to understand real risk in context. - An expanding AI data footprint
AI initiatives introduce new data stores, transient datasets, and training pipelines that are difficult to govern using traditional controls. - Slow incident response and alert fatigue
Limited context leads to excessive alerts, delayed prioritization, and slower response when data exposure occurs.
These challenges are not isolated technical issues they reflect a broader mismatch between how data environments operate today and how they are being secured.
A shift toward data centric security
In response, many organizations are reassessing their approach and moving toward data-centric security models that focus on the data itself rather than the infrastructure surrounding it.
This shift is driving increased interest in Data Security Posture Management (DSPM) - an approach designed to continuously discover, classify, and assess sensitive data across complex environments.
Rather than relying on assumptions, DSPM enables organizations to establish factual answers to fundamental questions:
- What sensitive data do we have?
- Where is it stored?
- Who can access it?
- How is it being used especially by AI systems?
By operating continuously, DSPM reflects the reality that cloud and AI environments change minute by minute, not quarter by quarter.
What effective DSPM looks like in practice
When implemented well, DSPM provides value across several dimensions:
- Continuous Discovery, Mapping and Automated Classification in DSPM solutions continuously reveal where sensitive data resides across shadow IT, fragmented data sources, and sprawling environments, closing critical visibility gaps that would otherwise weaken an organization’s security posture and reduce security teams ability to prioritize.
- Data Governance is the most important feature that a DSPM solution provides as it enables organizations to secure and monitor all sensitive data as well as changing their cultural mindset when it comes to data.
- AI Data Management enhances AI data governance by continuously discovering sensitive data across AI generated ephemeral stores and AI datasets, accurately classifying it across fragmented and sprawling environments using automated ML driven methods. It also prioritizes AI related incidents through context rich data sensitivity insights and enforces governance across the full AI data lifecycle.
- Access Monitoring provides continuous visibility into who has access to sensitive data and how it’s being used, monitoring interactions, anomalies, and risky behaviors by detecting misconfigurations, excessive permissions, and abnormal access patterns, including those from AI agents.
- Compliance reporting aligning policies with regulatory standards such as GDPR and HIPAA, providing automated compliance checks and simplifying audits. They also support detailed access reviews, retention reporting, and activity logs to help organizations demonstrate adherence to governance requirements and investigate compliance.
- Policy Unification Across Security Domains as the evolution of DSPM technology has enabled real-time policy evaluation during infrastructure provisioning with dedicated templates through policy engines that check data protection violations before resource creation. Developers receive immediate feedback when infrastructure-as-code configurations would create datastores failing to meet encryption, access control, or geographic residency requirements.
According to Gartner, from 2026, more than 20% of organizations will deploy DSPM technology, due to the “urgent requirements to identify and locate previously unknown data repositories and to mitigate associated security and privacy risks."
Why integration matters
One important lesson emerging from early DSPM adoption is that data security cannot operate in isolation. Context matters.
Understanding whether data exposure is truly risky often requires insight into identity, infrastructure configuration, workload behavior, and application context. Without this, organizations risk generating noise rather than clarity.
As a result, DSPM is getting aligned with broader cloud native security architectures, ensuring data insights are enriched with operational and identity context and can be acted on more effectively.
From capability to adoption
Integration alone, however, does not guarantee outcomes. As DSPM capabilities mature, many organizations are discovering that technology must be embedded into operating models, governance structures, and day-to-day security workflows to deliver sustained value.
Successful adoption typically follows certain principles which are listed below:
Establish a complete view of the data estate
DSPM adoption starts with comprehensive data mapping. Moving from static inventories to continuous discovery enables organizations to uncover shadow data and maintain an accurate view of sensitive information across cloud, SaaS, and hybrid environments.
Translate data into actionable intelligence
Classification and labelling transform raw data into meaningful security signals. By identifying which data is sensitive and why, organizations can automate controls, support compliance requirements, and ensure security systems understand business risk context.
Align access with data risk
Role based access control helps organizations manage exposure at scale. Mapping data sensitivity to clearly defined roles rather than individual permissions support least privilege access and simplifies ongoing governance.
Create cross functional ownership
DSPM touches security, privacy, compliance, cloud, and operations. Establishing a governance forum ensures alignment on ownership, priorities, and remediation paths, and prevents data risk from becoming siloed.
Integrate DSPM into existing security frameworks
DSPM delivers the greatest value when connected to broader security and operational tooling. Integration with SIEM, SOAR, DLP, IAM, and cloud platforms allows organizations to move from visibility to automated response, without disrupting existing processes.
Maintain audit ready evidence by design
Continuous audit trails, access logs, and compliance evidence help organizations shift from reactive audits to ongoing assurance. Standardized integration with logging and forensic workflows supports both regulatory requirements and incident investigations.
Over time, organizations that treat DSPM purely as a tooling initiative tend to stall. Those that succeed recognize it as an ongoing discipline rather than a one time deployment. It represents a shift in mindset, from static assurance to continuous control.
Moving from visibility to control
Organizations that succeed tend to focus on:
- Establishing clear ownership across security, privacy, cloud, and compliance
- Aligning data classification with business risk rather than technical taxonomy
- Integrating DSPM insights into existing security and operational workflows
- Treating data governance as an ongoing leadership responsibility
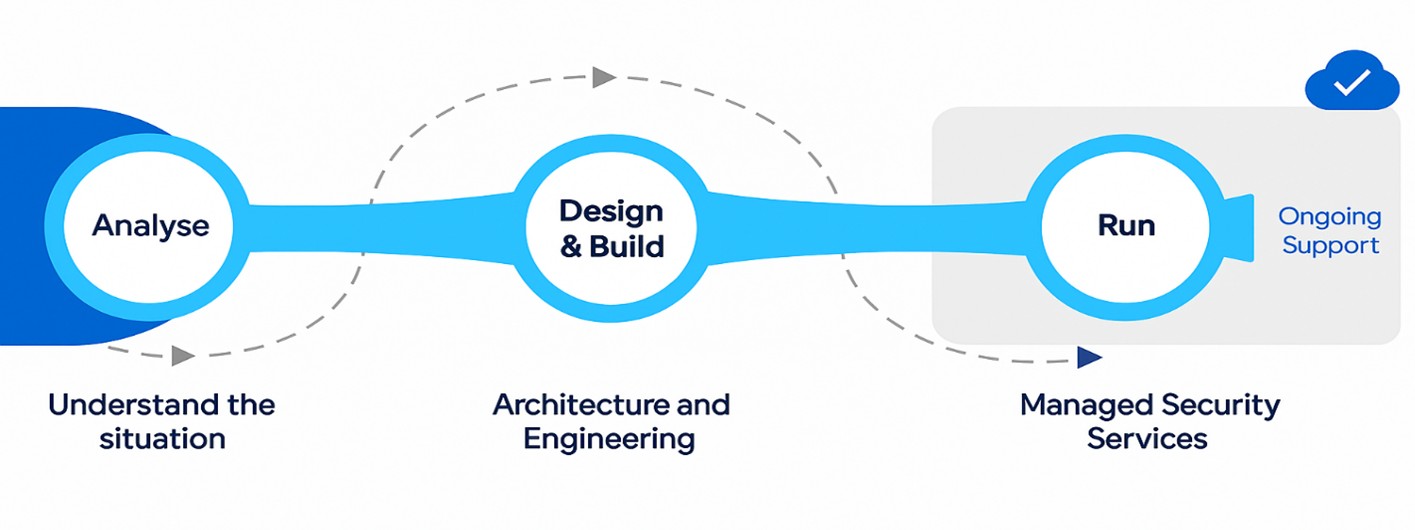
Atos Perspective and Structured Methodology
 Data has become one of the most valuable, and most exposed, assets organizations manage. As cloud, AI, and regulatory pressures continue to converge, maintaining trust will increasingly depend on the ability to demonstrate real, continuous control over sensitive data.
Data has become one of the most valuable, and most exposed, assets organizations manage. As cloud, AI, and regulatory pressures continue to converge, maintaining trust will increasingly depend on the ability to demonstrate real, continuous control over sensitive data.
From Atos perspective, treating data governance as a core business discipline, supported by integrated, data-centric security approaches, is becoming essential for organizations that want to innovate confidently while remaining resilient in an uncertain digital landscape.
Discover how Atos helps organizations navigate data security and trust at scale, more on our website.
Categories
Related posts
- Zero trust architecture and interoperability: Why tools alone don’t deliver security
- NIS2, DORA, CISA, SAMA: Why zero trust became the security standard regulators agree on
- Mythos outside, agents inside: The zero trust answer to AI on both sides of the firewall.
- Zero trust architecture explained: Why attackers don’t break in anymore. They log in



