The proliferation of cloud security features
What’s better, a CSP native or a third-party security tool? Why is it so important for Cloud Service Providers to offer their customers both these options for controlling their cybersecurity functions? In this article, we will examine the pros and cons of each, and how to make the right decision for your business.
The shared responsibility model
There is an abundance of literature on the cloud service provider (CSP) shared responsibility model. In previous blogs, I have introduced the concept in April 2019, followed by a deeper dive into IAM and encryption in October 2020.
When using a major CSP, the question to ask yourself now is not, “‘Is my cloud secure?” but rather, ”Am I using the cloud securely?”. Perhaps the most important element to consider when responding to the latter question is whether or not your capacity to secure your environment is in the cloud itself… In other words, you must have the capability (organization, resources, processes and tools) to continuously minimize the possible misconfigurations and their impact.
First, according to the NIST cybersecurity framework, you must:
- Gain visibility into your clouds and their configurations to identify the associated risks and potential threats
- Implement security controls to protect your environment and mitigate the risks you don’t want to maintain
- Detect any security incident as fast as possible
- Respond to security incidents in a timely manner
- Recover from security incidents and continuously learn to improve your cloud security posture
This is obviously a complex undertaking that requires organized human resources with proper processes and tools to automate the steps above as much as is feasible.

According to the Fortinet 2021 Cloud Security report, the top two barriers to faster cloud adoption are lack of visibility (53%) and control (46%).
CSP native security features
Large markets have developed around Cloud security, but third parties that provide CASB, CSPM, CWPP[i] and other cloud security features, have certain limitations. They either:
- Are limited by the APIs the CSPs make available from their environments, or
- Provide the controls externally, which often reduces the agility of the cloud security environment.
A CSP’s choice of APIs for providing features to external cybersecurity tools for controlling and automating the five NIST cybersecurity framework functions quickly became a differentiating factor. On the other hand, CSPs started to provide the capabilities through native cybersecurity features as well.
Indeed, CSPs are best positioned to provide you with the right tools to secure your data and workloads in the cloud, even though it is your responsibility to configure those tools and ensure the security of your data and workloads. When native to the CSP, cloud security controls are more tightly integrated in the cloud IaaS, PaaS or SaaS, so they have lower impact on the agility and performance of the cloud environment itself. Also, some features might be available natively only, so not exposed through APIs for external security tools to use.
[i] *CASB (Cloud Access Security Broker), CSPM (Cloud Security Posture Management), CWPP (Cloud Workload Protection Platform) are markets gathering certain set of features providing Cloud customers with control over their Cloud Security
Should you consider external security features?
Why not?
Well, Cloud adoption and migrating your business applications and features to a third party like a CSP is a question of trust, and you surely trust the CSP you have chosen… up to a point.
Segregation of duties is another crucial concept to consider in cybersecurity.
As much as possible, you might want to remove the ability of a provider (cloud or non-cloud) to monitor and control itself, for many reasons such as:
- Your most sensitive data and workloads might sit beyond the limit of the trust you have in the CSP
- The flaws and vulnerabilities, you want to cover with your cybersecurity controls, might impact CSP services and their native security features as well
- Some third parties might offer better and simpler to use cybersecurity features and management consoles
- It may be wiser to apply some controls from outside the cloud environment, such as the identity provider (IdP) feature for access management
- Regulatory compliance reasons
- To avoid the complexity of using multiple consoles for a cybersecurity control in a multi-cloud approach
- The controls may need to cover hundreds of SaaS applications as well
- Any other good reason you might have…
Using external cybersecurity controls might however compromise some technical and/or business features of your CSP or affect performance. CSPs are continuously extending their capabilities, so some of the above reasons may no longer be relevant in the future. For example, recognizing the rise of multi-cloud approaches, CSP started offering integration of other CSP security APIs from their own native tools (for example, Azure Sentinel can pull logs from GCP to create common security playbooks for the Azure tenant and GCP projects).
Striking a difficult balance
So, which drivers should prevail? Choosing between a native CSP security tool or an external third-party security tool should be guided by three main factors:
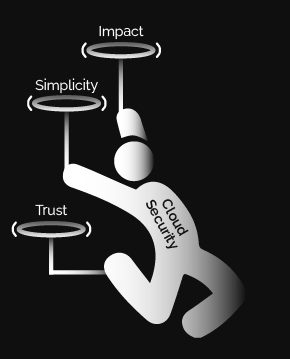
-
Trust
Need for control
Segregation of duties -
Simplicity
Better usability
Stronger governance -
Impact
Loss of options/features
Lowering performance
The trust driver will push you towards choosing an external control, whereas the impact driver will favor CSP-native controls. The simplicity driver sits in between, varying for every control.
Depending on your strategy and resources, the choice may vary. CSP-native features may simplify some cybersecurity controls, but an external solution can serve as a single pane of glass for all your environments. This could be a wiser approach, given the scarcity of cybersecurity and cloud skills.
Making the right choice, is where Managed Security Services Providers, experienced in Cloud security, might be of great help.
According to the State of Cloud Security Risk, Compliance, and Misconfigurations, CSA 2021, 59% of organizations consider lack of knowledge and expertise as the primary barrier to general cloud security.
About the author

Vasco Gomes
Global CTO for cybersecurity products, Distinguished Expert, Atos
Member of the Atos Scientific Community
Coming from an Information Technology engineering background, with 20 years’ of experience in information security, Vasco has helped many customers balance operational constraints versus acceptable business risks. In the recent years he has expanded this experience to help customers look into what the information security landscape might be in the next 5 years+ and best way to manage it. During innovation workshops, he shares with them some keys to anticipate the future shape of cybersecurity and maximize sovereignty over their most critical data.
Using those customer interactions and by continuously monitoring major technological trends, Vasco influences Atos cybersecurity services and products roadmaps, as well as partnerships, mergers and acquisitions.
