Malicious Proxyware Campaign Distributed via Microsoft Store
Report summary
Atos Threat Research Center uncovered a proxyware campaign spreading through the Microsoft Store. Attackers published several apps that look like normal tools (such as auto‑clickers or cleaners), but secretly turn user machines into residential proxy nodes.
Screenshot of Microsoft Store page for malicious application
The apps work as expected, which helps build trust. In the background, however, they load a hidden malicious DLL named “client.dll”, inside the same process through the Node.js FFI module. This means no suspicious child processes and no obvious signs for security tools to flag. After installation malware executes automatically on system startup using built-in MSIX startup tasks, which avoids leaving standard forensic artifacts like registry Run keys.
Once running, the app quietly connects to attacker infrastructure, gets instructions, and begins routing internet traffic through the victim system. There are no hardcoded servers and all communication is encrypted, making the activity look like normal app traffic.
The underlying model is quite simple: the infected host registers with a central server, receives relay endpoints, and acts as a proxy exit node for external traffic. The victim system becomes the point where requests are executed, effectively masking the origin of that traffic behind its IP.
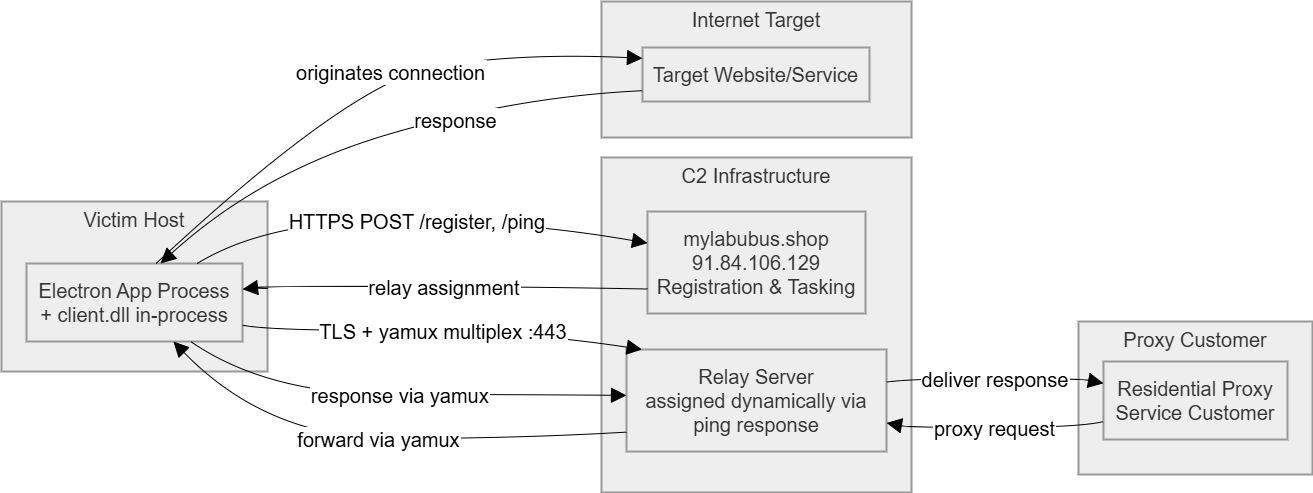
Network Architecture graph
The design is simple but effective. The malware does not steal data or function as a RAT – it only runs proxy traffic. This keeps its behavior low-profile and harder to detect.
All apps were signed and passed the Microsoft Store certification process showing that trusted platforms can still be abused. Security tools initially did not raise alerts. The campaign was only discovered through Atos threat hunting, based on unusual network connections.
Overall, this case shows how attackers can stay under the radar by hiding inside normal-looking applications distributed through trusted channels and behaving just “benign enough” to avoid detection.



