The transformative power of AI in the Security Operations Centers landscape
Accelerating SOC transformation with AI
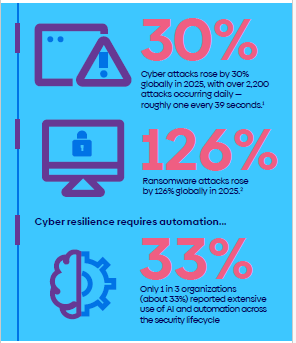
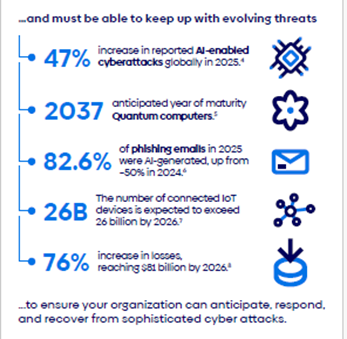
In 2025, organizations reported a 47% increase in AI-enabled cyberattacks. In parallel, attack surfaces kept expanding as IT environments grew in complexity with cloud ecosystems, SaaS applications, and widespread remote work models. In this constantly expanding cyber-threat context, Security Operations Centers (SOCs) are facing unprecedented operational pressure, and need to reinvent their work models.
Traditional SOC solutions are built on static detection rules, investigation and response playbooks, and SOAR-based automations. More advanced platforms now incorporate AI capabilities. Atos has been a pioneer in this shift towards AI for SOC, embedding AI-driven detection and triage to its MDR service, as early as 2020.
We are now entering the next phase of the SOC transformation journey, where AI is shifting from being used in the SOC to becoming the cornerstone of the SOC.
Key challenges in the SOC
- Alert saturation
SOC analysts must investigate significant volumes of events with a risk of alert fatigue. SOC classic approaches involve tuning detections to reduce volumes, as well as measuring and reducing false positives. However, these techniques must be applied carefully as they can be counterproductive in terms of protection: Threats can slip under the radar.
- Static detections approaches
Rules and signatures-based detections struggle to keep up with the growing sophistication of threats.
- Triage and investigation adaptability
Triage and investigation can require time-consuming, multi-step procedures. SOAR solutions can help automate steps, but their main drawback is that they rely largely on predefined playbooks. The end-result is a substantial maintenance effort, but also a lack of adaptability in case of a small behavioral deviation of a threat or in case of a new threat.
- Shortage of skills
Skilled SOC analysts are in global shortage. Analysts’ skills and time must be saved to focus on client risks, proactive threat management and on strong incident response.
AI-augmented managed detection and response approaches
In 2020, Atos integrated AI at the heart of its SOC strategy, reinforcing each stage of the detection and response lifecycle. AI is not replacing analysts — it enables faster detections, triage and investigations but also more confident decision-making. SOC can focus on client risks, detection tuning, proactive threat hunting and response.
Here are some of the key applications of AI for SOC:
- Smarter, more adaptive detections
AI-enhanced detection identifies anomalies, behavioral deviations, and weak malicious signals that traditional log-correlation rules might miss. The expansion of AI/ML-enabled security tools—such as EDR, XDR, WAF, SASE, and mail gateways—has resulted in a growing decentralization of detection. The Atos SOC acts as a security control tower, responsible for analyzing and correlating not only large volumes of logs but also intelligent alerts raised by a range of AI-augmented security tools.
- Intelligent triage
One of the most impactful AI contributions to SOC is the ability to distinguish noise from priority, thus refocusing SOC analysts’ efforts on the few alerts revealing likely malicious behavior.
Atos uses the following AI-driven scoring models to triage alerts:
- Severity and technical indicators
- Business-critical asset exposure
- Known patterns from historical SOC activity
This prioritization accelerates response times putting a few alerts in SOC’s priority bucket for immediate attention.
- Natural language AI assistant
Natural-language search capabilities help analysts navigate vast security datasets and client context information with ease. Some of these use cases are as follows:
- Analysts can search quickly within logs and alerts — “Were there any alerts related to this IP over the last 20 days?”
- Analyst can search through documentation, knowledge bases, or threat intelligence data — “Is this user a known VIP?” or “Is this a known malicious URL?”
Faster searches and ease of knowledge access lead to faster, more consistent investigations.
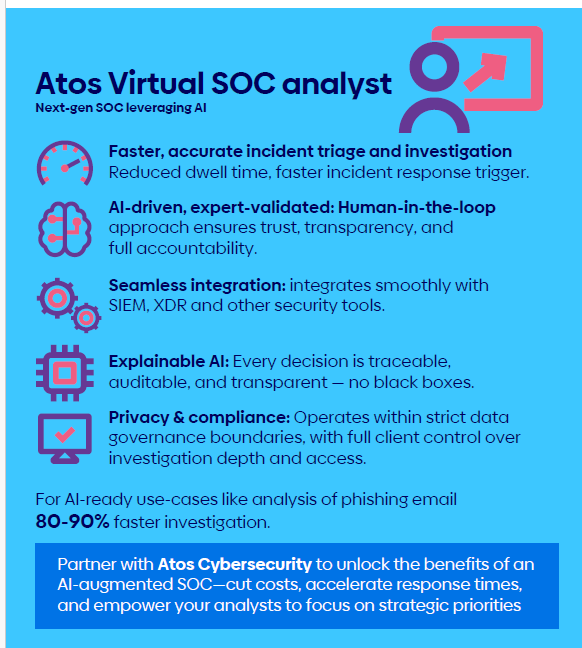
- The next SOC AI augmentation with Atos’ Virtual SOC Analyst
Use of AI for SOC is now reaching a turning point with the development of Agentic AI. Atos introduced the Virtual SOC Analyst powered by Qevlar AI. This innovative solution is designed to triage and investigate routine and medium-complexity alerts.
Here are some of the benefits of Atos’ Virtual SOC Analyst:
- Increased triage efficiency, quickly pointing our false positives or benign alerts
- Alert investigation actions such as enrich alerts, search logs, query security tools, and a check against Threat Intelligence
- A comprehensive alert investigation report with full transparency and audit trail of investigation steps
- Adjustments to client risks and context via inputs collected and provided by Atos expert SOC analysts during onboarding, regular client reviews, and via the analysis of past true and false positives
- Recommendations of incident response steps for the human SOC analyst to review and take over. This can include pointing out steps the AI Agent could not execute because of missing access.
These amazing benefits then raise the question: Why did Atos introduce the Virtual SOC Analyst?
Primarily, this was in response to the need to enable SOC teams to scale effectively in response to a rising volume of threats and associated alerts. refocus analyst workload on proactive threat hunting, advanced incident responses, and continuous detection tuning, such as high value and impact actions.(ie higher impact proactive actions)
Debunking the myth: AI misconceptions and risks
Atos is conscious that AI comes with many misconceptions and risks. With the current buzz around AI, these tend to be downplayed but there are certain aspects that they should keep in mind.
The myth of a fully autonomous AI SOC analyst
Human oversight and keeping strong technical and security expertise at SOC level remain key to protect organizations efficiently.
Atos’ experience shows that AI proves to be very efficient to investigate alerts such as a failed logins or reported phishing attempts. In the phishing use case, the Virtual SOC Analyst iteratively analyze the sender, URLs, attachments, compare with Threat Intelligence information, or even detonate a file to check if it is malicious. Assuming the same investigation was performed fully manually, this translates into 80-90% of the time saved for the SOC analyst for this specific use case.
Atos’ experience, though, is that results do not scale across all alert types or client environments. Efficiency can vary greatly depending on threat use cases but also depending on access to IT systems that have been granted to the AI solution.
Mitigating AI risks with responsible AI
one of the largest risks of AI is hallucination and invalid alert investigations, especially a false negative that leads to missing malicious activities. To mitigate these risks, Atos embeds Responsible AI principles across deployments to ensure transparency, fairness, and oversight. This ensures AI strengthens — rather than compromises — trust in SOC operations.
Responsible AI for the Virtual SOC Analyst includes:
- Human-in-the-loop: Humans approve or review impactful actions and oversee responses.
- Model auditability and traceability: Every AI-driven investigation comes with full audit trail and associated data such as hash, suspicious IP and reason why.
- Continuous tuning and validation: Analysts refine models and reinforce best practices. They also bring client- specific contextual information – the AI will not provide uniform outputs but adjust to clients.
- Use of Qevlar AI graph technology to avoid hallucinations
In addition to the above, Atos also actively manages risks around data protection and security. This includes strong regulatory alignment such as with the EU AI Act for compliance and for ethical use of automation.
The AI-augmented SOC of tomorrow
AI is a key driver in enhancing threat detection and response capabilities, enabling SOC to match pace with threats of growing volumes and sophistication. But this is a race. In the hands of malicious actors, AI can fuel cyberattacks too.
The optimal model is a smart balance of AI-powered detection, triage, alert investigation and assisted response combined with skilled analyst oversight. Virtual SOC Analysts will increasingly assist SOC analysts, improving responsiveness, consistency across 24×7 shifts and adaptability.
This race is also about growing and retaining strong expertise to understand risks, define detections, perform threat hunting, and respond to complex incidents. As a managed security services provider (MSSP), Atos helps clients shift to a more proactive defense, in careful consideration that SOC services will evolve to encompass continuous threat exposure management (CTEM). This means SOC will expand from detection and response, to monitoring and reducing exposure.
This is already happening, and AI simply accelerates this convergence.
>> Connect with us to learn more about how Atos’ Virtual SOC Analyst is poised to help augment your SOC’s resilience and working model.
>> Build resilient cyber defenses. Get started today with Atos: https://atos.net/en/services/cybersecurity.