The anatomy of modern IT supply chain attacks
The foundation of modern business — trust between organizations and their technology partners — has become a powerful weapon in the hands of cybercriminals. Supply chain attacks exploit these trusted relationships to bypass even the strongest defenses.
Today’s enterprises unknowingly rely on a fragile digital ecosystem, with an average of 112 SaaS applications and countless software dependencies, creating an expansive, interconnected attack surface.
What began as simple physical disruptions has evolved into highly sophisticated, software-based campaigns. Threat actors quickly realized that compromising a single supplier could grant access to thousands of downstream organizations. High-profile incidents like SolarWinds and MOVEit have proved the devastating potential of this tactic, making supply chain attacks one of the most persistent threats in cybersecurity.
Game for three: The threat actor, the supplier and the victim
Supply chain attacks occur when cybercriminals infiltrate a target organization by compromising its suppliers, vendors, or service providers. Rather than attacking the primary target directly, adversaries exploit the implicit trust placed in third parties to bypass robust internal defenses.
Threat actors
The threat landscape is dominated by several key actor categories, each with distinct motivations, capabilities, and targeting strategies.
- Organized criminal groups: Financially motivated syndicates running cybercrime as a business — monetizing breaches through scalable ransomware, extortion, and data theft
- State-sponsored actors: Espionage-driven APTs targeting critical infrastructure, government systems, and software vendors to steal intelligence and maintain long-term access. Out of these, 28% also pursue financial gains alongside espionage.
- Specialized cybercriminals:
- Initial access brokers sell network entry points to other actors.
- Credential harvesters steal and monetize corporate credentials.
- Vulnerability exploiters weaponize zero-days for targeted compromises.
According to Verizon, 54% of ransomware victims in 2025 had credentials in public dumps — a clear sign of access broker involvement.
Suppliers
Supply chain attackers target suppliers offering maximum operational advantage and widespread impact. Vendors with large customer bases and elevated system privileges, like IT management, security, and remote access tools, are prime targets, enabling attackers to bypass defenses and gain admin-level access. Cybercriminals exploit trusted relationships, compromising update mechanisms, valid certificates, and communication channels to discreetly deliver malicious code. Additionally, attackers focus on suppliers providing critical services or widely-used software, including popular open-source packages, to infiltrate multiple industries and regions at once.
Victims
The reality of supply chain attacks is that virtually any organization can become a victim. From multinational corporations to small local businesses, from government agencies to non-profit organizations, from healthcare providers to educational institutions, no entity is immune to these sophisticated threats.
As supply chain attacks continue to surge by 431% since 2021, organizations of all types and sizes must recognize their vulnerability and implement comprehensive supply chain security measures.
Understanding the key players in supply chain attacks – the threat actors, the suppliers they target and the victims – lays the groundwork for examining their historical progression. The below evolution showcases how these adversaries have refined their tactics, consistently exploiting the vulnerabilities within the digital supply chain to achieve greater scale and impact over time.
The evolving landscape of supply chain attacks
2020: SolarWinds Breach
- State-sponsored attack sets new precedent.
First major alert to global supply chain vulnerabilities.
2021–2022: Expansion by Crime Groups
- Criminal actors diversify vectors.
Exploits: MOVEit, 3CX, Log4j show dependency abuse.
2023–2024: Third-Party Surge
- Third-party breaches up 68%.
Tools targeted: TeamCity, Okta, Zero-days.
Rise of APT & ransomware groups.
2025: Edge & Identity Attacks
- Credential & edge device focus.
- Snowflake breach, 54% victims in dump sites.
Supply chain attacks have evolved rapidly since 2020. The SolarWinds breach marked a shift to sophisticated state-sponsored campaigns. By 2021-22, organized crime groups expanded attack vectors, exploiting MOVEit, 3CX, and Log4j dependencies. In 2023-24, breaches via third-party providers surged 68%, with APTs and ransomware actors exploiting TeamCity, Okta, and zero-day flaws. By 2025, specialized actors intensified credential theft and targeted edge devices, with platforms like Snowflake compromised and 54% of ransomware victims exposed in credential dumps.
This timeline mirrors the growing scale, interconnectivity, and threat actor diversity driving modern supply chain attacks. We explore these critical attack techniques and their progression through the lens of the MITRE ATT&CK framework, offering a standardized view of real-world adversary behaviors.
Navigating key attack vectors
Modern supply chain attacks leverage a diverse range of vectors, each introducing unique risks to enterprise security. Understanding these vectors — and the operational consequences if breached — is essential to building resilient defenses.
1. Software supply chain attacks (MITRE ATT&CK technique # 002)
Risk: Compromising software updates or development pipelines is an attack method classified as T1195.002 in the MITRE ATT&CK® framework. This allows threat actors to distribute malicious code across thousands of customer environments simultaneously. Incidents like SolarWinds showed how a single breach can trigger global operational, reputational, and financial fallouts.
Recommendations: Enforce code signing, validate update sources, and as a method for identifying and tracking all third-party components in your software stack. This improves transparency and enables rapid response when vulnerabilities in third-party libraries or dependencies are disclosed.
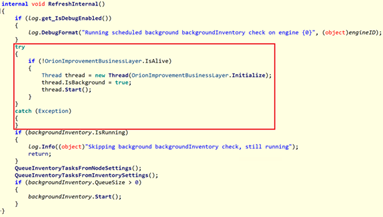
2. Open-source component attacks (MITRE ATT&CK technique # 001)
Attacker adds backdoor to PyPI’s Warehouse GitHub repo
PyPI’s Infrastructure Upgraded
Packages uploaded to PYPI are replaced with malicious packages
Python users install malicious packages from PYPI
Risk: Malicious code introduced via third-party open-source libraries can silently infect development pipelines and applications, often going undetected until exploitation occurs. Popular attack techniques include typo squatting and dependency confusion. These tactics are classified under T1195.001 in the MITRE ATT&CK® framework, which documents real-world adversary techniques used to compromise software supply chains. This technique is especially dangerous because it targets trusted developer workflows, enabling attackers to plant backdoors in widely used software with minimal visibility.
Recommendations: Implement automated dependency scanning, restrict unverified libraries, and monitor critical repositories for suspicious packages or unauthorized changes. These measures help reduce exposure to hidden threats in your software supply chain, improve response time when vulnerabilities are disclosed, and maintain the integrity of your development environment.
3. Service Provider Attacks (MITRE ATT&CK technique # T1199)

Risk: Breaching a managed service provider (MSP) or cloud vendor gives attackers privileged access to multiple downstream clients. This enables credential theft, lateral movement, and disruption of critical systems. This tactic — classified as T1199 in the MITRE ATT&CK® framework — involves exploiting trusted third-party relationships to compromise otherwise well-defended environments. It’s particularly dangerous because attackers can bypass perimeter defenses by abusing legitimate connections between service providers and their customers.
Recommendations: Continuously audit third-party access, enforce multi-factor authentication (MFA) for all privileged accounts, and maintain incident response plans for third-party or supply chain breaches.
4. API and Credential Exploitation (MITRE ATT&CK technique # TA0001)
Credentials
- Passwords:
- Passw@rd
- password
- pwd
- pass
- credentials
- company123!
- Certificates:
- machine certificate
- pfx
- Password vault:
- .kdb
- .kdbx
- QR codes
Accounts
- Administrator
- Built-in domain admin
- admin accounts (obtained during discovery phase of the attack)
Access
- rdp
- rdweb
- VPN
- citrix
Business
- customer list
- customer
- cust list
- Precise names of customers
Risk: Compromised APIs and stolen credentials are among the most common entry points for attackers today. This tactic falls under TA0001 – Initial Access in the MITRE ATT&CK® framework, which outlines how adversaries infiltrate target environments. By leveraging leaked credentials or misconfigured APIs, attackers can bypass perimeter controls and authenticate as legitimate users, often moving undetected across systems. These breaches can quickly cascade across supply chains if access is reused or federated across partners.
Recommendations:
- Enforce strict credential hygiene. Prohibit shared accounts, use password vaults, and regularly rotate secrets.
- Rotate and monitor API keys, especially for third-party integrations.
- Adopt a zero trust architecture with adaptive, context-aware authentication and strict least-privilege access controls.
- Continuously audit exposed services and identity access logs to detect misuse early.
5. Edge Device & Repository-Based Attacks(MITRE ATT&CK techniques # T1200 & # T1552.001)
Risk: Attackers increasingly exploit vulnerable edge devices and leaked credentials in public repositories to gain initial access into supply chain environments. These techniques, categorized under T1200 (Hardware Additions) and T1552.001 (Unsecured Credentials in Code Repositories) in the MITRE ATT&CK® framework, bypass traditional security perimeters by targeting weak operational hygiene, such as unpatched routers, exposed IoT gateways, or hardcoded credentials in Git repositories. These entry points are often overlooked in routine assessments yet offer high-impact, low-resistance paths for adversaries to move laterally or inject malicious updates across environments.
Recommendations:
- Regularly patch and monitor all internet-facing infrastructure, including edge and IoT devices.
- Continuously scan public and private code repositories for leaked secrets using automated tools.
- Enforce secure coding and peer review practices to eliminate hardcoded credentials before code is committed.
Strengthening your supply chain defenses
Supply chain attacks have rapidly evolved into one of the most persistent and complex threats facing modern businesses.
This article explored the anatomy of these attacks, which centers around three interconnected elements: the actors behind the attacks, the suppliers they exploit, and the diverse attack vectors they leverage.
At the core are the threat actors from organized cybercriminal groups to state-sponsored APTs and specialized access brokers, each with distinct motivations but a shared objective: to exploit trusted relationships and maximize operational and financial gain. Their primary targets are suppliers and service providers, chosen for their elevated access, privileged system connections, and extensive customer ecosystems. A successful breach of a single supplier can trigger a ripple effect across thousands of connected organizations.
These attacks are executed through increasingly sophisticated vectors, including compromised software updates, manipulated open-source packages, third-party service provider breaches, credential theft, exposed APIs, and vulnerabilities in edge devices and cloud infrastructure. Each vector introduces unique risks, from operational disruption and data compromise to large-scale, cross-industry infiltration.
Aleksander Pawlicki
Global Product Director, Head of Threat Research Center, Atos
View detailsof Aleksander Pawlicki >






